Key Takeaway
- Private information is a PR risk, not just a legal issue; one leak can damage trust faster than any compliance penalty.
- PDPA Malaysia sets the baseline for personal data, but real protection comes from internal processes, staff behaviour, and vendor control.
- Employees are often the weakest link, especially through WhatsApp, personal email, and unmanaged cloud storage.
- The Personal Data Protection (Amendment) Act 2024 raised the stakes, introducing DPO appointments, mandatory breach notification, and data portability, with phased commencement in 2025.
- Crisis response determines brand survival: not just whether a breach happens, but how you communicate it.
Table of Contents
ToggleMalaysian companies today operate in an environment where private information flows constantly between teams, systems, and external partners. Customer records, employee files, and business documents are accessed, shared, and stored across multiple platforms every day.
Many incidents don’t start with movie-style hacking. They start with everyday behaviour: sharing an Excel file in a WhatsApp group, forwarding work documents to a personal email address, or granting vendors broader access than necessary.
Once that happens, the problem escalates quickly beyond internal operations. It becomes a matter of public trust.
Handling off-the-record information effectively is no longer just a compliance task. It is a business function that sits at the intersection of operations, human behaviour, legal responsibility, and public perception.
What Counts As “Private Information” In Malaysia?
Private information includes any data that can identify individuals or expose sensitive operations. Many companies underestimate how much of this data they handle daily.
In practice, off-the-record information usually falls into three buckets:
- Personal data (PDPA focus): Names, phone numbers, email addresses, NRIC numbers, and delivery details
- Sensitive personal data (higher risk under PDPA): Health information, biometric data, religious beliefs, and similar categories
- Confidential business data (not always PDPA, still high risk): Contracts, pricing structures, internal reports, client databases
Important nuance: PDPA regulates personal data (including sensitive personal data) processed in commercial transactions. The JPDP also states the Act does not apply to the Federal Government and State Governments, and includes other scope exclusions. That means purely non-personal confidential business information is not “PDPA data” unless it contains personal identifiers, but it can still trigger major reputational and commercial fallout if leaked.
| Type | Example | Risk Level | Common Leak Scenario |
|---|---|---|---|
| Personal data | Phone number, email | Medium | Marketing list shared externally |
| Sensitive personal data | Medical / biometric data | High | Employee over-shares internally |
| Business data | Contracts, pricing | High | Employee sends file via personal email |
A simple example highlights the risk: a tuition centre storing student registration forms in a shared cloud folder may unintentionally expose hundreds of records if access is not properly controlled.
Why Private Information Is A PR Issue, Not Just A Legal Issue
Many companies approach PDPA as a regulatory checklist. In reality, customers respond more strongly to trust signals than compliance status.
When off-the-record information is mishandled, the consequences often unfold quickly:
- Customers begin to question the company’s reliability
- Screenshots and complaints circulate on social media
- Negative sentiment spreads across platforms
- Media attention becomes a possibility
- Competitors gain an opportunity to position themselves as safer alternatives
For example, if an eCommerce company exposes delivery data, even briefly, customers may hesitate to place future orders. The financial impact comes not only from potential penalties but from a PR crisis which results in lost confidence in your brand.
And the legal expectations are no longer “soft.” The Amendment Act adds explicit obligations (like mandatory data breach notification and formal DPO accountability) that increase scrutiny when something goes wrong.
What Does PDPA Malaysia Require Companies To Do?
The PDPA outlines seven core principles that guide how personal data should be handled. The JPDP lists these principles and expects organisations to apply them in real operations, not just in a document folder.
| Principle | Practical Meaning |
|---|---|
| General | Collect data only for a valid purpose |
| Notice and choice | Inform users how their data will be used |
| Disclosure | Do not share data without proper basis |
| Security | Protect data from unauthorised access |
| Retention | Do not keep data longer than necessary |
| Data integrity | Ensure accuracy of records |
| Access | Allow individuals to review their data |
Many compliance gaps occur when these principles are not translated into workflows.
What Changed Under The PDPA Amendments?
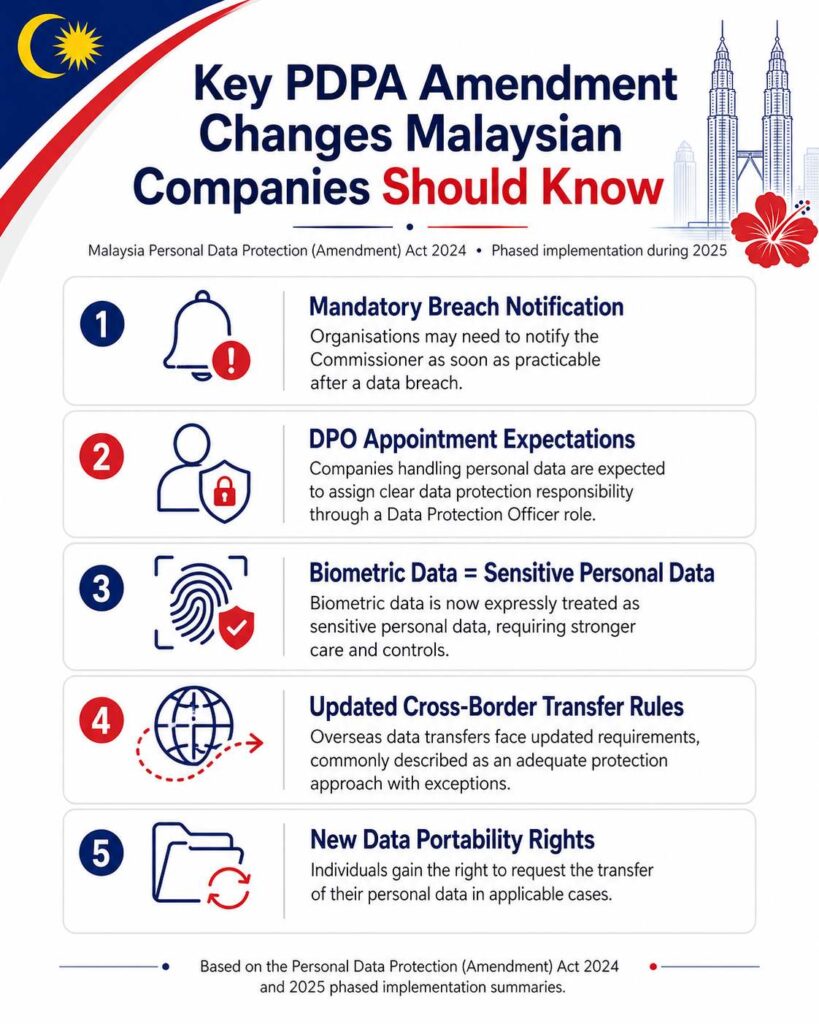
The Personal Data Protection (Amendment) Act 2024 shifted expectations significantly. Data protection can’t be treated as “set and forget.”
Key updates include:
- Mandatory breach notification requirements
- Stronger expectations around Data Protection Officer (DPO) appointment and responsibilities
- Biometric data explicitly treated as sensitive personal data
- Updated cross-border transfer expectations (commonly summarised as moving toward an “adequate protection” approach, with exceptions)
- Introduction of data portability rights
These changes mean companies must actively monitor, manage, and report how data is handled, and they must be ready to explain themselves publicly when an incident happens.
Who Is Responsible For Handling Private Information?
Data protection is a shared responsibility across the organisation:
- Management sets direction, budget, and accountability
- Compliance / DPO roles oversee policies, evidence, and enforcement
- Employees interact with data daily and carry the highest operational risk
- Vendors extend exposure beyond internal systems
| Role | Risk Level | Example |
|---|---|---|
| Management | Strategic | No enforcement, no resourcing |
| Employees | High | Sharing data via messaging apps |
| Vendors | High | Data leak through external systems |
In many cases, incidents originate from employee actions or vendor access rather than “technical failure.”
When Are Companies Most At Risk?
Risk increases during routine processes, especially when people are rushing:
- Customer onboarding and data collection
- Internal data sharing and reporting
- Employee resignation or termination
- Vendor onboarding and system access
- Incident handling and response
A common scenario: a sales employee exports customer contacts before leaving the company. Without controls (and offboarding discipline), this can become significant exposure.
Where Does Private Information Typically Leak?
Leaks often happen through convenience-driven behaviour:
- Sharing customer details in WhatsApp groups
- Using personal email or personal cloud storage for work files
- Storing sensitive data in unsecured spreadsheets
- Accessing data through shared office devices
- Using unmonitored USB drives
These practices bypass internal safeguards and create preventable risk.
How Should Companies Handle Private Information?
A structured approach reduces both compliance and reputational risk.
Collect Only What You Need
Avoid collecting unnecessary data. Every data point should have a clear purpose. Communicate the purpose and obtain consent where required.
Control Access Internally
Limit access based on roles. Monitor access and sharing. Remove access immediately when employees leave or change roles.
Secure Data Properly
Encrypt sensitive information. Enforce strong authentication and passwords. Avoid storing company data on personal platforms.
Train Employees
Training should be practical, not theoretical: what not to forward, where not to store files, how to confirm recipients, and what “sensitive” looks like in day-to-day work.
Manage Vendors Carefully
Assess vendor security before sharing data. Use contracts that require safeguards, limit access, and define incident reporting expectations.
Set Data Retention Policies
Define how long data should be stored. Delete or anonymise records that are no longer needed. Review retention regularly.
Prepare A Breach Response Plan
Have a clear plan to identify, contain, and respond to incidents, plus a comms plan to prevent confusion, mixed messaging, and reputational collapse.
How Should PR Teams Respond To A Data Leak?
How you communicate after a data incident often determines long-term impact. With breach notification expectations now formalised under the amended PDPA, “no comment” is not a strategy.
| Stage | Action |
|---|---|
| Acknowledge | Confirm awareness promptly |
| Investigate | Understand the situation before making claims |
| Communicate | Provide clear and transparent updates |
| Support | Assist affected individuals |
| Update | Continue sharing progress |
Common mistakes include delaying communication, issuing vague statements, over-denying early, or shifting blame. A delayed or unclear response can escalate the situation even if the breach is limited.
Tip: Prepare two templates in advance ((1) “initial holding statement” and (2) “confirmed facts update”) and require Legal + DPO review before release.
Challenges Malaysian Companies Face
Several challenges make data protection difficult to implement effectively:
- Limited awareness of the amended PDPA obligations
- Over-reliance on informal tools (messaging apps and spreadsheets)
- Lack of structured internal policies and evidence trails
- Insufficient vendor oversight
- A perception among SMEs that they are not targets
These problems are often operational, not purely technical.
Read More: How PR Builds Customer Loyalty in Malaysia
Costs Of Getting It Wrong
The impact of mishandling private information extends beyond legal penalties.
| Cost Type | Impact |
|---|---|
| Regulatory | Fines, enforcement actions, mandated remediation |
| Customer | Loss of trust and loyalty |
| PR | Crisis management expenses, reputational recovery |
| Operational | Downtime, distracted teams, disrupted delivery |
| Long-term | Brand damage, reduced competitiveness |
In many cases, the long-term trust impact costs more than the legal response.
Practical Checklist For Malaysian Companies
- Create or refresh a privacy policy aligned with PDPA
- Confirm PDPA scope for your organisation (commercial transactions; public sector exemptions)
- Appoint clear responsibility (often via DPO function)
- Map how data flows inside the organisation
- Restrict access based on roles (and log access where feasible)
- Review vendor agreements and access permissions regularly
- Conduct employee training with real examples (WhatsApp, spreadsheets, personal email)
- Develop a crisis communication plan and run tabletop simulations
Handling Private Info The Proper Way
Handling private information in Malaysia requires more than compliance with PDPA. It requires a system that integrates policy, behaviour, technology, and communication to protect trust at every level.
For organisations looking to strengthen reputation management and crisis readiness, working with experienced PR professionals can provide valuable support. At PRESS PR Agency, Malaysia’s number one PR agency, we help brands navigate sensitive situations, manage public perception, and respond with clarity through strategic PR services.
Sources
- Department of Personal Data Protection (JPDP): PDPA principles; PDPA scope and non-application; PDPA FAQs
- Personal Data Protection (Amendment) Act 2024 (Malaysia)
- Baker McKenzie (Insight+): summary of phased commencement dates during 2025
- Crowe Malaysia: summary of phased rollout across early 2025
- Tay & Partners: “countdown to compliance” timeline discussion
- Mayer Brown: analysis referencing breach notification obligations from June 2025
- DLA Piper “Data Protection Laws of the World”: Malaysia overview and amendment themes
Frequently Asked Questions About Off-The-Record Data Protection in Malaysia
What Is PDPA Malaysia?
PDPA is Malaysia’s main law regulating how organisations handle personal data in commercial transactions, including collection, use, disclosure, security, and retention (as described by the JPDP).
Why Is Private Information Important For Businesses?
It directly affects customer trust, legal compliance, and brand reputation, making it a core business risk, not a “back office” issue.
Do SMEs Need To Comply With PDPA?
In general, yes, if they process personal data in commercial transactions. The JPDP notes the Federal and State Governments are exempt, and certain processing may fall outside PDPA’s scope.
What Is The Most Common Cause Of Data Leaks?
Many incidents start with human-driven mistakes (misdirected sharing, weak access controls, personal email use, and informal storage) rather than advanced attacks.
Do Companies Need A Data Protection Officer?
The amended PDPA introduces formal DPO expectations. Even where requirements depend on how the law is applied to your organisation, it is increasingly expected, especially for organisations processing large volumes of personal data.
How Should Companies Respond To Data Breaches?
Act quickly: contain, investigate, communicate clearly, support affected individuals, and keep stakeholders updated. Under the amended PDPA, breach notification duties can apply, so delaying or staying vague can create legal and reputational problems.


